We help enterprises and startups design, develop, and scale security-focused applications — from real-time threat detection platforms to automated compliance monitoring systems. Our focus: speed, resilience, and measurable protection against evolving cyber threats.
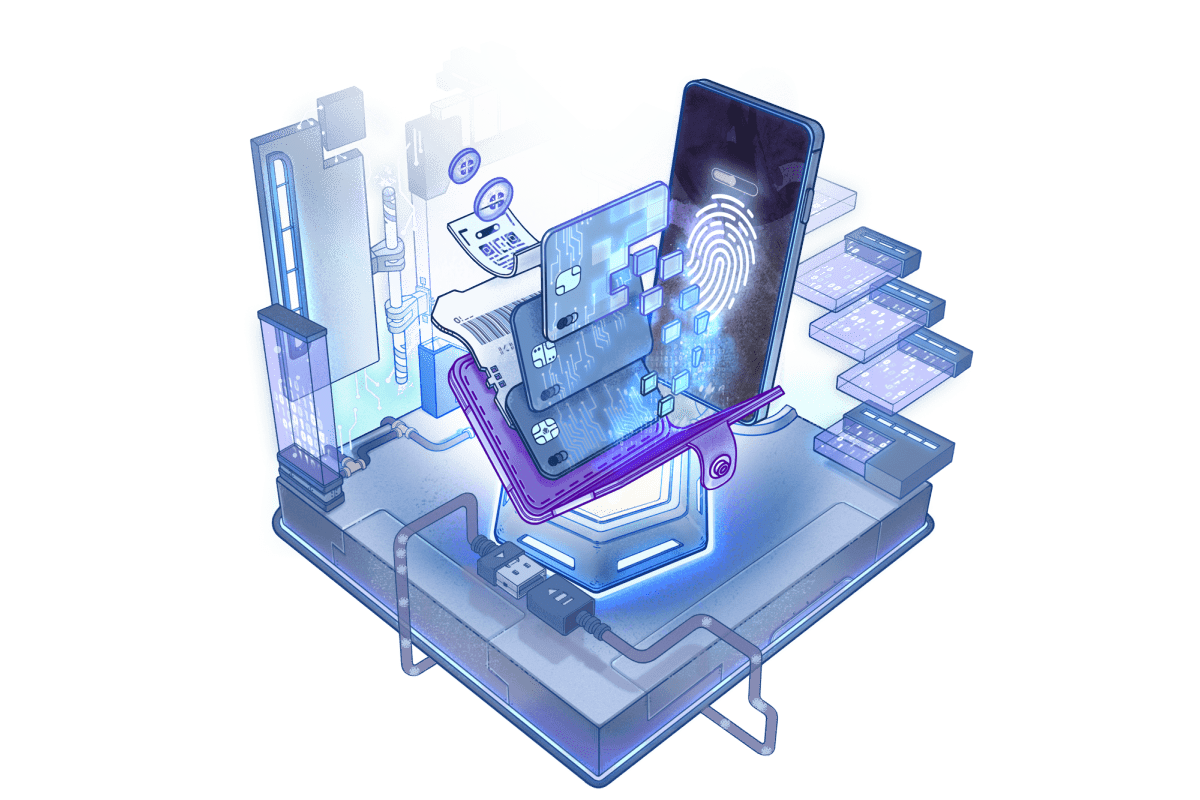
Custom-built cybersecurity platforms are redefining how organizations detect threats, manage compliance, and protect sensitive data. From automated incident response to unified monitoring, tailored solutions unlock new levels of security, efficiency, and control.

At Lasting Dynamics, security and compliance aren’t add-ons — they are embedded in the architecture of every cybersecurity solution we build. From secure identity management to continuous threat monitoring, our platforms align with global and regional regulations such as GDPR, CCPA, PCI DSS, HIPAA, and ISO 27001. We ensure that your systems protect sensitive data, maintain audit readiness, and foster trust with clients and stakeholders from day one.



We don’t just develop cybersecurity platforms — we deliver measurable resilience.
Our solutions produce tangible results across incident response, vulnerability management, and compliance readiness. These are some of the key performance improvements our clients have achieved.
Our clients rely on custom-built cybersecurity platforms to enhance threat detection, strengthen compliance, and secure mission-critical systems. From AI-powered vulnerability scanning to integrated incident response workflows, these case studies show how our tailored solutions deliver measurable security improvements in real-world environments.
We combine a robust set of modern security technologies with a proven development methodology to deliver reliable, scalable, and future-ready cybersecurity platforms. From SIEM integration and identity management to automated compliance reporting, our approach ensures protection, speed, and quality at every step.
We follow a rigorous, step-by-step methodology to deliver secure, scalable, and compliant cybersecurity platforms — from early discovery to deployment and ongoing optimization. Every phase is designed to minimize risk, accelerate incident response, and ensure regulatory readiness.
Explore in-depth articles on cybersecurity development, threat detection, compliance automation, and secure software architecture.
Stay ahead with expert strategies, penetration testing guides, and technical deep-dives from our team.



It’s a tailored security platform designed to meet your organization’s unique needs, integrating threat detection, compliance, and monitoring into one solution.
Most of our projects go live within 3–6 months, depending on complexity and integrations.
Yes, we connect with SIEMs, IAM platforms, and vulnerability scanners to create a unified security dashboard.
We design software aligned with GDPR, CCPA, PCI DSS, HIPAA, and ISO 9001 requirements.
We provide ongoing monitoring, patch management, and upgrades to adapt to emerging threats.